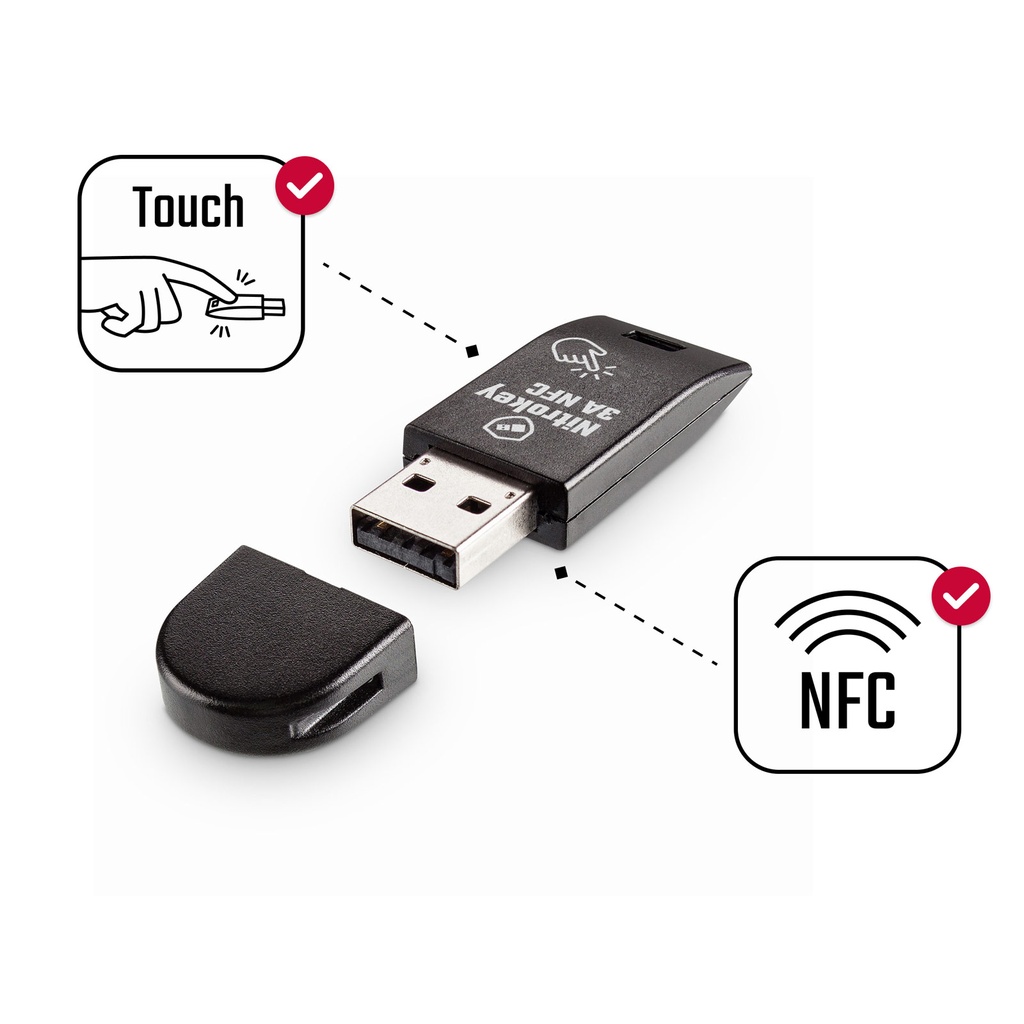
Nitrokey 3A NFC
The New Nitrokey 3 With NFC, USB-C, Rust, Common Criteria EAL 6+
The new Nitrokey 3 is the best Nitrokey we have ever developed. It offers NFC, USB-A for the first time. The Nitrokey 3 combines the features of previous Nitrokey models: FIDO2, one-time passwords, OpenPGP smart card, Curve25519, password manager, Common Criteria EAL 6+ certified secure element, firmware updates. This reliably protects your accounts against phishing and password theft, and encrypts your communications and data. With strong hardware encryption, trustworthy thanks to open source, quality made in Germany.
IMPORTANT NOTE: The included Secure Element is not used at this time. We are currently working on its integration and will enable its use later via firmware update.Use Cases
For private and corporate use - protection against mass surveillance and hackers
Passwordless login
Forget your password to log in to Microsoft services (e.g. Office 365) and Nextcloud and use Nitrokey for passwordless login instead.Protect online accounts using two-factor authentication (2FA)
Nitrokey is your key to secure login to websites (e.g. Google, Facebook; overview at www.dongleauth.com). Using FIDO2, FIDO U2F, or one-time passwords (OTP), your accounts remain secure even if your password is stolen.Phishing protection
When using FIDO, the respective domain is automatically checked and users are effectively protected against phishing attacks.Mobile usage with smartphones
Using FIDO and NFC, you can also securely access your accounts on Android and iPhone smartphones.Encrypt data and emails
Encrypt your emails with GnuPG, OpenPGP, S/MIME, Thunderbird or Outlook. Encrypt entire hard drives using TrueCrypt/VeraCrypt, LUKS or individual files using GnuPG. Your private keys are securely stored in Nitrokey and cannot be exported/stolen.
For companies - protection against hackers and industrial espionage
Passwordless logon to Windows 10 computers
Employees will be able to log in to their Windows 10 Pro computers managed by Azure Active Directory without passwords. All that is required is a Nitrokey 3.Passwordless login to your own enterprise systems
Replace your password policy, unauthorized password slips and costly password resets with passwordless login with the Nitrokey 3. Security and acceptance through simplicity. We are happy to advise you on integration.
For IT administrators and security experts - protect critical infrastructure
Administering servers securely with SSH
Always have your SSH key securely with you in Nitrokey. Your key is PIN protected and cannot be exported/stolen from the Nitrokey. This eliminates the insecure and annoying synchronization of key files on client systems.Protect Internet of Things (IoT) and own products
Protect your own hardware products by integrating Nitrokey. Ideal for remote maintenance and ensuring product authenticity.Store cryptographic keys securely
Store cryptographic keys and certificates securely in Nitrokey, preventing their theft.Protect computer BIOS integrity
Using the Nitrokey and Measured Boot, the integrity of the computer BIOS/firmware is verified. The colored LED of the Nitrokey signals whether the BIOS has integrity (green) or whether tampering has been detected (red). Compatible e.g. with NitroPads.
Functions
FIDO U2F, FIDO2 for passwordless login
FIDO sets new standards in easy usability and thus achieves high acceptance. FIDO reliably protects your accounts against password theft and phishing.Disabled passwords to protect accounts against identity theft
Protect your accounts against identity theft. One-time passwords are generated in Nitrokey and serve as a second authentication factor for logins (in addition to your normal password). Thus, your accounts remain secure even if your password is stolen.Secure cryptographic key storage
Store your private keys for encrypting emails, hard drives or individual files securely in Nitrokey. This way they are protected against loss, theft and computer viruses and are always with you. Key backups protect against loss.Password Manager
Store your passwords securely encrypted in the integrated password manager. This way you always have your passwords with you and they remain protected even if you lose your Nitrokey.Integrity Check / Tamper Detection
Verify the integrity from the computer BIOS using Verified Boot. The Nitrokey's colored LED indicates whether the BIOS has integrity (green) or tampering has been detected (red). Supported computers require a BIOS based on Coreboot and Heads such as the NitroPad.
Security Technology
The Nitrokey 3 is based on a novel security architecture:
All firmware is developed in the memory-safe programming language Rust. This avoids potentially security-critical memory errors.
The firmware is based on the framework Trussed developed in Rust, which is designed for security-critical embedded systems and developed in cooperation with our partner SoloKeys. Among other things, Trussed implements cryptographic operations. Of course, the code is published as open source.
The hardware is based on the LPC55S6x or nRF52 microprocessor, which has numerous security features, such as Secure Boot, ARM TrustZone, Physical Unclonable Functions (PUF).
Additionally, a Secure Element (SE050), quasi a smart card, is used for the cryptographic memory. This has been security-certified up to the operating system level according to Common Criteria EAL 6+ and thus also meets high security requirements. Due to the power requirement, the secure element can only be used via USB but not via NFC.
As with all Nitrokey developments, Nitrokey 3 is open source, so the secure implementation can be reviewed by anyone.
Supported Systems and Interfaces
Operating Systems: Windows, macOS, Linux, BSD, Android, iOS
Interfaces: Microsoft CSP, OpenPGP, S/MIME, X.509, PKCS#11, OpenSC, FIDO2, FIDO U2F
Overview of some websites with two-factor authentication on www.dongleauth.com
Technical Details
Authentication standards: WebAuthentication (WebAuthn), CTAP2/FIDO2, CTAP1/FIDO U2F 1.2, HMAC-Based One-Time Password (RFC 4226), Time-Based One-Time Password (RFC 6238)
Two-factor authentication and passwordless login for unlimited number of accounts (FIDO U2F, FIDO2)
Signed firmware updates
With touch button
Certification of the tamper-proof secure element according to CC EAL6+
Secure key storage: RSA 2048-4096 bit or ECC 256-521 bit, AES-128 or AES-256
Elliptic curves: NIST P-256, P-384, P-521 (secp256r1/prime256v1, secp384r1/prime384v1, secp521r1/prime521v1), Ed25519/Curve25519, Koblitz (192-256 bit), brainpoolP256r1, brainpoolP384r1, brainpoolP512r1
External hash algorithms: SHA-256, SHA-384, SHA-512
One-time passwords: HOTP (RFC 4226), TOTP (RFC 6238), HOTP checking
Physical random number generator (TRNG)
Activity indicator: four-color LED
Hardware interfaces: USB 1.1, type A or type C, NFC
Compliance: FCC, CE, RoHS, WEEE, OSHwA